Technology
10 Expert-Recommended Practices for Hybrid Cloud Security Management
Introduction
A significantly more effective model has appeared on the horizon in the form of the hybrid cloud as an answer to the question of how to possess scalability and flexibility while maintaining effective control over the organization’s resource usage. Organizations should use private and public cloud structures, which help minimize costs and improve efficiency. However, this structure brings different security complexities to the table. Security amid a hybrid cloud was once a luxury that could be ignored; it has become necessary. Hybrid Cloud Security Management protects INFO from security breaches, legal non-compliance, and new threats from cloud vulnerabilities.
In this guide, you will discover 10 best practices for handling key issues of hybrid cloud security management suggested by experts to maximize the benefits of using a hybrid cloud architecture at your business.
Understanding the Complexities of Hybrid Cloud Security
Hybrid cloud security challenges stem from the diverse nature of these environments. Common pain points include:
1. Lack of Control and Visibility: It is often challenging to fully control and monitor hybrid cloud environments. To manage security properly, networks and systems are spread across various providers and organizations, leaving gaps in which malicious actions are hard to notice.
2. Data Sovereignty Issues: The hybrid cloud may have some parts in one or multiple countries with different data sovereignty rules and regulations. Effectively managing these transfers and complying with these regulations poses a daunting task.
3. Environment Interoperability Issues: Accessing one environment from the other usually involves an API call or using middleware, which triggers security issues. Hybrid environments are particularly vulnerable to dangers rooted in misconfiguration of API and integration, and the latter’s usage is often insecure.
4. Hybrid Setup Threats: Organizations with a hybrid cloud model become vulnerable to malicious and involuntary insider threats. Those with IT rights to view or edit restricted information or those with rights to process information unsuitably pose a threat intentionally or through incompetence.
These characteristics mean a strong demand for best practices that will help keep Hybrid Cloud Security strong.
What are the Best Practices for Hybrid Cloud Security Management?
Explore the top best practices for hybrid cloud security management given below:
1. Organization and individual security assessments should be conducted.
Understanding the vulnerabilities of a hybrid cloud environment starts with thorough security assessments. Regular assessments help identify weak points, define security baselines, and formulate actionable solutions.
- Evaluate risks related to data storage, access, and integration points.
- Use tools designed for hybrid cloud ecosystems to perform these evaluations.
Pro Tip: Schedule assessments before and after significant transitions, such as system upgrades or migrations.
2. Standardize Security Policies Across Environments
Hybrid environments require consistent security policies to avoid misconfigurations. Centralized management positions them for success as they span on-premises and cloud systems.
- Use policy management tools to enforce consistent data encryption and access controls.
- Regularly review policies to address evolving threats.
Case Study: Businesses implementing centralized policies have reported a 30% reduction in security breaches caused by misconfigurations.
3. Strengthen Authentication Mechanisms
Passwords alone are insufficient for hybrid cloud security. Employing solid alphanumeric passwords and using other security IDs, including passwords, also plays a key role in strengthening the authentication system, including MFA.
- Use biometric systems or token-based methods for enhanced security.
- Complement MFA with adaptive authentication to identify suspicious login attempts.
Industry Insight: Gartner predicts that MFA adoption will reduce identity-related attacks by 75% by 2025.
4. Leverage Continuous Monitoring and Auditing
Real-time monitoring ensures that security teams can detect and respond to threats swiftly.
- Deploy tools that provide unified visibility across all hybrid environments.
- Use AI-driven systems to analyze logs for anomalies and potential breaches.
Advanced Tip: Use it with regular review to ensure that your system complies with the current laws.
5. Prioritize Data Encryption
Data security is incomplete without encryption. To mitigate risks, data at rest and in transit must be encrypted.
- Adopt end-to-end encryption for sensitive workflows.
- All keys should be fully protected or even stored in an HSM to reduce risks as much as possible.
Best Practice: Implement tokenization for an additional layer of security to mask sensitive data in hybrid environments.
6. Strengthen Identity and Access Management (IAM)
RBAC is the foundation of most IAM systems today and has been described extensively in the literature. Restricting access reduces the threats from an insider threat or stolen credentials. The user roles should be clearly defined so permission is also granted based on the needs observed during business operations.
- User roles must also be defined as clearly as possible, and the permissions for every role should correspond to the project’s real functioning.
- Regularly audit access logs to identify and revoke outdated permissions.
Quick Tip: Integrating IAM with hybrid-compatible platforms ensures seamless functionality across systems.
7. Automate Security Configurations
Automation means that no mistakes will be committed, and security policies will be applied uniformly.
- Use Infrastructure as Code (IaC) solutions to standardize configurations.
- Automate tasks like firewall updates, compliance checks, and system patches.
Real-World Application: Automation is beneficial during cloud migration services, ensuring secure transitions without manual interventions.
8. Regularly Patch and Update Systems
This shows that outdated software is one of the easiest things for attackers to take down. Most of the time, it is essential to relieve the insecurity and apply updates and patches from the IT security team as a preventive measure.
- Establish a patch management schedule for all systems, including cloud services.
- Before general application, new tests should be applied in trial modes across the infrastructure.
Fact Check: According to a 2024 report, 43% of cloud-related breaches occurred due to unpatched vulnerabilities.
9. Provide Security Training for Employees
Accidents are still a significant factor that contributes to insecurity. A fundamental objective of hybrid cloud security training is to make employees the first line of defense.
- Focus training on recognizing phishing attacks, securing personal devices, and following best practices for Hybrid Cloud Security.
- Use simulated attack scenarios to test and improve employee response.
Training Tip: Reinforce learning with regular updates to reflect changes in security policies or threats.
10. Collaborate with Cloud Providers
Cloud providers play a crucial role in securing hybrid setups. Partnering with them helps organizations understand and optimize shared responsibility models.
- Use the provider’s tools for monitoring, compliance checks, and identity management.
- Clearly define roles and expectations in service-level agreements (SLAs).
Key Insight: Engaging providers during significant transitions, such as cloud migration services, can streamline security efforts.
Advanced Approaches to Hybrid Cloud Security
Beyond the basics, organizations can further security by adopting innovative strategies:
- Zero Trust Architecture: A Zero-Trust model ensures that every access request is verified regardless of origin, minimizing insider threats.
- AI-Powered Security Tools: AI enables predictive threat analysis, providing organizations with actionable insights before vulnerabilities are exploited.
- Enhanced Incident Response Plans: A detailed incident response plan tailored to hybrid environments ensures faster recovery from potential breaches.
Conclusion
The hybrid cloud offers unprecedented business opportunities but presents unique security challenges. Organizations can effectively secure their environments by following these best practices for Hybrid Cloud Security while enabling flexibility and scalability.
Hybrid Cloud Security Management is a dynamic process requiring continuous adaptation. Proactive measures like robust IAM systems, centralized policies, and employee training create a resilient security framework. Finally, partnering with providers during transitions like cloud migration services ensures seamless integration and optimal protection.
Following these approaches, businesses can now comfortably adopt hybrid cloud solutions since they open up their full potential for usage without exposing them to risks.
================================================================================
Author Bio
Chandresh Patel is a CEO, Agile coach, and founder of Bacancy Technology. His truly entrepreneurial spirit, skillful expertise, and extensive knowledge of Agile software development services have helped the organization achieve new heights of success. Chandresh is leading the organization into global markets systematically, innovatively, and collaboratively to fulfill custom software development needs and provide optimum quality.
Technology
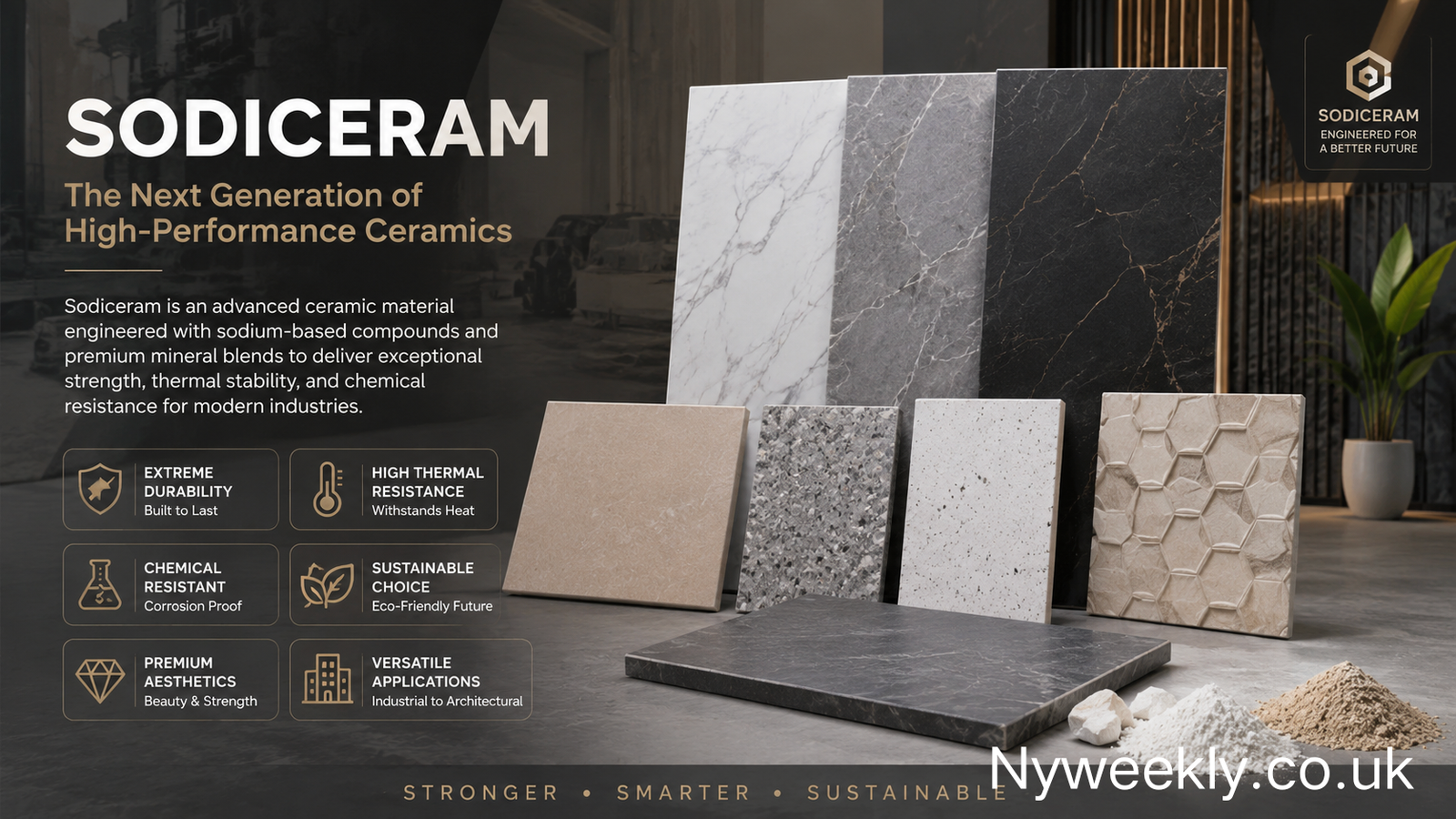
sodiceram and the Rise of High-Performance Ceramics
Introduction
Modern industries are under constant pressure to find materials that can survive extreme temperatures, resist chemical damage, last for decades, and still maintain visual appeal. Traditional ceramics have served humanity for thousands of years, but many industrial sectors now require something stronger, denser, and more adaptable. This demand has pushed advanced ceramic technologies into the spotlight, and one term increasingly associated with this evolution is sodiceram.
Although sodiceram is still an emerging concept rather than a universally standardized scientific classification, it is commonly described as a high-performance ceramic material enhanced with sodium-based compounds and engineered mineral blends. Its growing popularity comes from its ability to combine durability, thermal stability, chemical resistance, and architectural flexibility in a single material system.
What makes sodiceram especially interesting is that it sits at the intersection of engineering and design. It is not only being discussed in industrial manufacturing but also in architecture, energy systems, interior design, and sustainable construction. As industries move toward materials that deliver longer life cycles with lower maintenance demands, sodiceram has started attracting serious attention from engineers, architects, and manufacturers alike.
What Is sodiceram
Sodiceram refers to an advanced ceramic material or ceramic category designed to improve the limitations of traditional ceramics. Most descriptions of sodiceram emphasize the inclusion of sodium-based compounds within the ceramic matrix to improve strength, density, thermal resistance, and overall structural performance.
READ MORE: casîo and the Timeless Reinvention of Everyday Technology
Unlike conventional ceramics that are often made primarily for decorative or household purposes, sodiceram is generally associated with technical and industrial applications. During manufacturing, sodium compounds influence the vitrification process, helping the ceramic structure become denser and less porous. This change improves resistance to cracking, moisture absorption, and thermal stress.
Many modern interpretations of sodiceram also include advanced surface engineering. Manufacturers often combine the ceramic base with high-temperature firing methods, precision texturing, and reinforced mineral compositions. The result is a material capable of surviving conditions that would damage ordinary ceramic products.
Another reason sodiceram has gained attention is its versatility. It can appear in industrial machinery, laboratory surfaces, architectural facades, flooring systems, and high-traffic commercial interiors. Some producers even market sodiceram as a next-generation solution that balances aesthetics with structural reliability.
The Science Behind sodiceram
The technical appeal of sodiceram lies in how sodium compounds interact with ceramic materials during production. In conventional ceramics, firing temperatures and material density play critical roles in determining durability. Sodium-based additives can alter the internal structure during sintering and vitrification, allowing stronger bonding between particles.
This improved bonding produces a denser ceramic body with fewer microscopic pores. Lower porosity matters because porous materials are more vulnerable to water penetration, chemical degradation, and thermal shock. By reducing internal weaknesses, sodiceram becomes more resistant to cracking and long-term wear.
Another scientific advantage involves thermal stability. High-performance ceramics are valued because they maintain structural integrity under severe heat conditions. Sodiceram materials are often engineered to tolerate sudden temperature changes without expanding or fracturing excessively. This property makes them useful in industrial settings where temperature fluctuations are common.
Chemical resistance is another important characteristic. In laboratories, factories, and processing plants, surfaces are frequently exposed to corrosive substances. Sodiceram is often promoted as highly resistant to acids, alkalis, and industrial cleaning agents. This resistance helps extend operational lifespan while reducing maintenance costs.
How sodiceram Is Manufactured
The manufacturing process behind sodiceram combines traditional ceramic production with advanced engineering techniques. The process usually begins with refined mineral ingredients such as clay, feldspar, silica, quartz, and sodium compounds. These materials are carefully blended to create a consistent ceramic mixture.
Once the raw materials are prepared, the mixture undergoes shaping and compression. This stage determines the density and structural consistency of the final product. Precision is essential because even small inconsistencies can weaken ceramic performance.
The firing stage is where sodiceram develops many of its defining properties. Extremely high temperatures are used to trigger vitrification, a process that transforms the material into a hardened, glass-like structure. Sodium compounds help optimize this process by improving bonding and reducing unwanted porosity.
Modern production methods may also include laser finishing, textured surfaces, anti-slip coatings, and high-resolution printing technologies. These additions allow sodiceram to meet both technical and aesthetic demands. Some architectural products even replicate natural stone, marble, or wood textures while maintaining ceramic durability.
Manufacturers increasingly focus on sustainability during production as well. Some facilities now recycle water, reduce kiln emissions, and incorporate recycled materials into sodiceram formulations to minimize environmental impact.
Why sodiceram Is Becoming Important in Modern Construction
Construction industries worldwide are searching for materials that offer long-term reliability with lower maintenance demands. Sodiceram fits this need because it combines strength with design flexibility. Architects and builders are especially drawn to materials that can withstand weather exposure while preserving appearance over time.
Exterior cladding systems increasingly rely on advanced ceramics because they resist moisture, fading, and thermal stress better than many conventional materials. Sodiceram is often promoted for facade panels, wall coverings, and high-strength flooring systems.
Commercial spaces also benefit from the durability of sodiceram. Airports, shopping centers, hotels, and hospitals experience heavy foot traffic every day. Materials used in these environments must survive continuous use without deteriorating quickly. The dense composition of sodiceram helps reduce scratches, cracking, and surface wear.
Interior designers appreciate sodiceram for another reason: visual versatility. Modern ceramic engineering allows surfaces to imitate natural stone, polished concrete, or textured wood while offering easier maintenance and improved durability. This combination makes sodiceram attractive in both luxury and functional spaces.
Industrial Applications of sodiceram
Beyond architecture, sodiceram is increasingly discussed in industrial sectors where ordinary materials struggle under harsh conditions. Heavy manufacturing environments require materials capable of handling heat, pressure, abrasion, and chemical exposure simultaneously.
Industrial linings are one example. Processing plants often use ceramic materials to protect equipment from wear and corrosion. Sodiceram’s chemical stability and heat resistance make it suitable for these demanding applications.
Power generation facilities also benefit from advanced ceramics. High-temperature systems require insulation materials that maintain integrity under continuous thermal stress. Sodiceram can contribute to thermal shielding, protective barriers, and energy-efficient equipment systems.
The electronics industry has also shown interest in advanced ceramics because of their insulating properties. Certain ceramic compositions can provide thermal management and electrical insulation simultaneously, making them useful for specialized components.
In medical and laboratory environments, hygienic surfaces are essential. Low-porosity ceramic materials reduce contamination risks and simplify cleaning. Because sodiceram surfaces are often engineered to resist chemical damage, they can perform well in sterile or highly controlled environments.
The Environmental Side of sodiceram
One reason advanced ceramics are receiving increased attention is their potential contribution to sustainability. While ceramic manufacturing requires significant energy, the long lifespan of materials like sodiceram can offset environmental costs over time.
Durability plays a major role here. Materials that last longer reduce replacement frequency and lower construction waste. In many commercial buildings, replacing flooring or facade materials can be expensive and environmentally damaging. Sodiceram’s resistance to wear helps reduce this cycle.
Some producers also emphasize energy-efficient firing systems and recycled mineral content. Water recycling systems and reduced-emission kilns are becoming more common in advanced ceramic manufacturing.
Another environmental benefit is maintenance reduction. Surfaces that resist stains, chemicals, and moisture require fewer harsh cleaning agents over their lifetime. This can lower the overall environmental impact of maintenance operations in commercial and industrial spaces.
Challenges and Limitations of sodiceram
Despite its advantages, sodiceram is not without limitations. One important challenge is cost. High-performance ceramics require advanced manufacturing methods, controlled mineral compositions, and precision engineering. These factors increase production expenses compared to ordinary ceramic products.
Another limitation is brittleness under certain forms of stress. While sodiceram may have excellent compressive strength, ceramics in general can still be vulnerable to sudden impact or tension-related fractures. Engineers must carefully design installations to avoid concentrated stress points.
Standardization is another issue. Since sodiceram is still an evolving term rather than a universally regulated category, product quality can vary significantly between manufacturers. Some companies use the term broadly for marketing purposes, while others apply it to highly engineered ceramic systems.
Availability can also differ across regions. Advanced ceramic technologies are more accessible in some industrial markets than others, which can affect pricing and adoption rates.
The Future of sodiceram
The future of sodiceram appears closely connected to broader developments in materials science and sustainable construction. Industries are increasingly prioritizing materials that combine long operational life with reduced maintenance requirements. This trend strongly favors advanced ceramic technologies.
Researchers continue exploring improved ceramic formulations with enhanced thermal resistance, lighter weight, and greater fracture toughness. As manufacturing methods become more efficient, sodiceram products may become more affordable and widely available.
Architectural trends are also contributing to the growth of advanced ceramics. Modern buildings increasingly rely on high-performance surfaces that combine visual sophistication with environmental resilience. Sodiceram fits naturally into this movement because it offers both structural reliability and design flexibility.
There is also growing interest in smart surfaces and multifunctional materials. Some advanced ceramics now incorporate antibacterial coatings, anti-slip technologies, and heat-reflective properties. Future generations of sodiceram may integrate even more specialized functions into architectural and industrial systems.
READ MORE: adswynk com: Understanding Its Role in Online Advertising Platforms
Conclusion
Sodiceram represents a modern evolution in ceramic technology, combining traditional ceramic foundations with advanced engineering techniques and sodium-enhanced formulations. Its appeal comes from its ability to deliver strength, thermal stability, chemical resistance, and aesthetic versatility within a single material system.
Although the term sodiceram is still developing and lacks universal standardization, its growing presence across architecture, manufacturing, industrial engineering, and design reflects a broader shift toward high-performance materials. Businesses and builders are no longer satisfied with surfaces that simply look attractive. They increasingly demand materials capable of surviving harsh environments, reducing maintenance costs, and supporting sustainable construction goals.
The rise of sodiceram highlights how modern material science continues reshaping industries that once relied on conventional solutions. As research advances and manufacturing becomes more refined, sodiceram could move from a niche concept into a recognized category of next-generation ceramic materials.
FAQs
What is sodiceram mainly used for?
Sodiceram is commonly associated with industrial ceramics, architectural surfaces, flooring systems, facade panels, laboratory surfaces, and heat-resistant applications where durability and chemical resistance are important.
Is sodiceram different from traditional ceramics?
Yes. Sodiceram is generally described as a more advanced ceramic material that includes sodium-based compounds and engineered mineral compositions to improve strength, thermal resistance, and durability.
Why are sodium compounds important in sodiceram?
Sodium compounds help improve vitrification and particle bonding during manufacturing. This creates a denser ceramic structure with lower porosity and better resistance to heat and chemicals.
Is sodiceram environmentally friendly?
Many manufacturers promote sodiceram as a sustainable option because of its long lifespan, low maintenance requirements, and potential use of recycled materials and energy-efficient production methods.
Does sodiceram have any disadvantages?
The main disadvantages include higher production costs, possible brittleness under certain impact conditions, and the lack of universal standardization across manufacturers.
READ MORE: https://nyweekly.co.uk/
Technology
liopad and the Future of Flexible Creative Technology

Introduction
Technology products often disappear as quickly as they appear, yet some names continue circulating through online discussions because they trigger curiosity, experimentation, and speculation. One such name is liopad. While many emerging platforms fail to establish a recognizable identity, liopad has steadily attracted attention among users searching for flexible tools that combine accessibility, productivity, and entertainment into a single ecosystem.
Part of the growing interest around liopad comes from the way modern users interact with technology. People no longer want isolated systems that perform only one task. They prefer platforms that adapt to changing needs, whether those needs involve communication, streaming, content interaction, workflow management, or personal organization. This shift has created space for products like liopad to gain relevance in conversations about convenience and integrated user experiences.
Another reason liopad stands out is the mystery surrounding its broader capabilities. Unlike heavily marketed platforms that define themselves with rigid branding, liopad has developed an identity through user exploration and community-driven discussion. That organic growth has helped create a sense of intrigue. Users are not simply consuming a finished product; they are actively trying to understand how liopad fits into evolving online habits.
The growing visibility of liopad also reflects a broader trend in modern technology culture. Audiences increasingly value adaptability over complexity. They want smoother interfaces, responsive systems, and experiences that reduce friction rather than add layers of unnecessary functionality. In that environment, liopad represents more than just a name. It symbolizes the demand for platforms that feel lightweight, efficient, and capable of evolving alongside user expectations.
What Is liopad
liopad is commonly associated with an emerging technology-oriented platform experience designed to support flexible interaction across different forms of online activity. Depending on the context in which users encounter it, liopad may be connected with media access, productivity enhancement, collaborative tools, or personalized interface systems that prioritize simplicity and responsiveness.
READ MORE: soundgasm and the Rise of Intimate Audio Communities
What makes liopad particularly interesting is that it does not fit neatly into a single category. Some users describe it as a lightweight workspace environment, while others associate it with content access and cross-functional interaction. That ambiguity has actually contributed to its popularity because people interpret the platform according to their own needs rather than forcing themselves into a predefined system.
The architecture behind liopad appears to emphasize adaptability. Instead of overwhelming users with highly technical structures, the platform focuses on streamlined usability. This design philosophy aligns with current consumer behavior, where users increasingly reject bloated systems in favor of cleaner and faster experiences.
Another defining characteristic of liopad is its accessibility. Many modern platforms unintentionally create barriers through complicated onboarding processes or excessive interface clutter. liopad gains attention because it reduces those obstacles. Even users with limited technical knowledge often find the environment approachable, which broadens its potential audience considerably.
The Rising Popularity of liopad
The rapid increase in attention surrounding liopad is not accidental. It reflects larger shifts in how people consume online services and interact with connected platforms. Over the last few years, audiences have become more selective about the technologies they adopt. Speed, convenience, and intuitive functionality now matter more than flashy marketing campaigns.
liopad benefits from this shift because it aligns with modern expectations. Users increasingly prefer systems that integrate multiple capabilities into one manageable environment. Rather than switching between numerous applications, they seek platforms capable of handling several tasks with minimal complexity.
Social communities have also played a major role in expanding awareness of liopad. Online forums, discussion spaces, and user-generated content have contributed significantly to the platform’s visibility. When technology spreads through organic recommendations instead of aggressive advertising, it often develops stronger trust among users. People tend to believe practical experiences shared by real users more than promotional campaigns.
Another factor behind the popularity of liopad is curiosity. In an online environment saturated with predictable products, platforms that remain somewhat unconventional naturally attract attention. Users enjoy discovering tools that feel different from mainstream alternatives, especially when those tools offer practical advantages without demanding extensive learning curves.
How liopad Reflects Changing User Expectations
The success of modern platforms increasingly depends on their ability to adapt to changing consumer psychology. Users are no longer impressed solely by technical specifications. They care about emotional usability, meaning how comfortable and intuitive a platform feels during everyday interaction. liopad appears to resonate because it embraces that principle.
Many older systems were built around feature accumulation. Developers continuously added functions until platforms became unnecessarily crowded. This often resulted in confusing navigation and slower performance. liopad reflects a different philosophy by prioritizing balance over excess.
The modern internet user also values freedom. People want customizable experiences that adjust to individual preferences rather than forcing everyone into identical workflows. liopad appeals to this mindset by offering a more fluid interaction style that feels less restrictive than many conventional systems.
Another important shift involves attention span. Online audiences now process enormous amounts of information daily, which means patience for complicated interfaces has dramatically decreased. liopad appears designed with this reality in mind. Faster responsiveness and simplified interaction structures help maintain engagement without exhausting users mentally.
This emphasis on smoother interaction is especially important in younger audiences. New generations of users grew up with instant access to content and services. They expect platforms to function naturally from the first interaction. liopad benefits because it seems aligned with those expectations rather than relying on outdated design logic.
The Design Philosophy Behind liopad
One of the most discussed aspects of liopad is its apparent commitment to minimalism without sacrificing capability. Minimalism in technology is often misunderstood. It does not simply mean removing features. True minimalism involves presenting functionality in a way that feels effortless to the user.
liopad demonstrates this philosophy through cleaner interface structures and reduced visual clutter. Instead of overwhelming users with aggressive notifications or complex navigation layers, the platform appears focused on maintaining clarity and responsiveness.
This approach has practical advantages. Cleaner systems typically reduce cognitive fatigue, allowing users to remain productive for longer periods. Whether someone is browsing content, organizing tasks, or exploring media, a smoother interface improves the overall experience significantly.
Another notable design principle associated with liopad is flexibility. Traditional platforms often force users into fixed behavior patterns. liopad, however, seems to encourage adaptable usage. Different users can interact with the platform in different ways depending on their personal goals.
That flexibility is increasingly valuable in modern technology culture because user behavior itself has become more fluid. People constantly move between work, entertainment, communication, and information consumption throughout the day. Platforms capable of supporting those transitions naturally gain stronger relevance.
liopad and Cross-Platform Convenience
Cross-platform compatibility has become one of the defining expectations of contemporary technology users. People no longer operate within a single device ecosystem. They switch between smartphones, tablets, laptops, and desktop environments constantly. liopad appears positioned to support this interconnected lifestyle effectively.
The importance of continuity cannot be overstated. Users expect experiences to remain consistent regardless of which device they are using. Interruptions or compatibility issues quickly damage engagement. liopad benefits from emphasizing smoother transitions between platforms and environments.
This consistency also influences productivity. When users can continue tasks seamlessly across devices, workflow interruptions decrease dramatically. That capability becomes particularly valuable for students, remote workers, creators, and multitasking professionals who rely on continuous access throughout the day.
Another major advantage of cross-platform flexibility is accessibility. Not every user owns premium hardware. Platforms that function efficiently across different performance levels naturally attract broader audiences. liopad appears to recognize this reality by emphasizing accessibility rather than exclusivity.
Security and User Trust in liopad
Modern users are far more aware of privacy and security concerns than previous generations. High-profile data breaches and widespread tracking practices have made audiences cautious about how platforms manage personal information. Any growing platform must address these concerns effectively to maintain credibility.
liopad gains attention partly because users increasingly prioritize systems that feel transparent and user-focused. Trust is no longer created through branding alone. It depends on consistency, responsiveness, and clear operational behavior.
Security also extends beyond technical protection. Emotional trust matters equally. Users want confidence that platforms will remain stable, reliable, and respectful of their experience. Excessive advertising, intrusive tracking, and manipulative engagement tactics often damage long-term loyalty.
Platforms like liopad benefit when they maintain a cleaner relationship with users. Simpler systems often feel safer because they reduce unnecessary complexity and make user interaction more understandable.
The future success of liopad may depend heavily on how effectively it continues balancing accessibility with security. In today’s environment, users expect both convenience and protection simultaneously. Achieving that balance remains one of the biggest challenges in modern technology development.
Why Communities Matter to liopad
Technology platforms rarely survive through software alone. Communities play a massive role in shaping long-term relevance. liopad has benefited from growing discussions among online users who share experiences, recommendations, and discoveries related to the platform.
Community-driven growth is powerful because it creates authenticity. Users feel more connected to platforms that evolve through shared exploration rather than corporate messaging. This kind of engagement often results in stronger loyalty and more meaningful interaction.
Communities also help platforms improve organically. Feedback cycles become faster and more practical when real users actively discuss strengths and weaknesses. liopad appears to benefit from this dynamic because conversation around the platform remains active and exploratory.
Another important aspect of community culture is adaptability. Online communities constantly reinterpret platforms according to emerging trends and needs. That flexibility can extend the lifespan of technology products far beyond their original purpose.
As liopad continues evolving, its relationship with user communities will likely remain one of its most important strengths. In modern internet culture, engaged communities often matter just as much as technical innovation itself.
The Future Potential of liopad
Predicting the future of any emerging platform is difficult because technology landscapes change rapidly. However, liopad possesses several characteristics that position it well for continued relevance. Flexibility, accessibility, and user-centered interaction are no longer optional advantages. They are essential requirements for long-term growth.
One of the most promising aspects of liopad is its ability to remain adaptable. Platforms that define themselves too narrowly often struggle when user behavior changes. liopad benefits from a broader identity that allows it to evolve alongside shifting expectations.
The increasing demand for lightweight, responsive experiences also works in liopad’s favor. Users are becoming more selective about where they invest attention and time. Systems that reduce friction while maintaining capability are likely to dominate future online interaction.
Another factor supporting the future of liopad is cultural fatigue with overcomplicated ecosystems. Many users feel overwhelmed by platforms packed with unnecessary features, aggressive monetization strategies, and intrusive engagement tactics. liopad represents a cleaner alternative that feels more focused on usability than excess.
If the platform continues refining its strengths while maintaining community trust, liopad could establish itself as a meaningful presence within the evolving technology landscape.
READ MORE: crackstreams and the Culture of Free Sports Streaming
Conclusion
liopad represents more than a passing online trend. It reflects changing expectations about how technology should function in everyday life. Users increasingly value simplicity, adaptability, accessibility, and trust over excessive complexity. Platforms that understand these priorities are far more likely to maintain relevance in an increasingly competitive environment.
What makes liopad particularly compelling is its flexibility. Instead of forcing users into rigid patterns, it appears to support diverse forms of interaction while maintaining a cleaner and more approachable experience. That balance between functionality and simplicity is difficult to achieve, which explains why interest in liopad continues to grow.
The platform also demonstrates how modern communities influence technological success. Organic discussion, shared exploration, and user-driven visibility have all contributed to the expanding recognition of liopad. In many ways, its growth reflects the power of collective curiosity within modern internet culture.
As technology continues evolving, platforms that prioritize smooth interaction and meaningful usability will likely shape the next phase of online experiences. liopad stands as an example of how adaptable systems can attract attention by focusing on what users genuinely need rather than overwhelming them with unnecessary complexity.
FAQs
What is liopad mainly used for?
liopad is commonly associated with flexible online interaction, including productivity support, content access, and streamlined user experiences across multiple environments.
Why is liopad becoming popular online?
liopad is gaining attention because users increasingly prefer simple, adaptable, and responsive platforms that reduce unnecessary complexity and improve convenience.
Is liopad suitable for beginners?
Yes, liopad appears designed with accessibility in mind, making it approachable even for users who do not have advanced technical knowledge.
What makes liopad different from traditional platforms?
Unlike many conventional systems, liopad emphasizes flexibility, cleaner interfaces, and smoother usability instead of overwhelming users with excessive features.
Can liopad continue growing in the future?
liopad has strong potential for future growth because modern users increasingly value adaptable and user-centered technology experiences.
READ MORE: https://nyweekly.co.uk/
Entertainment
crackstreams and the Culture of Free Sports Streaming

Introduction
Sports broadcasting has changed dramatically over the last decade. Fans no longer gather only around cable television packages or expensive subscription channels to watch major events. Today, millions of viewers search online for quick access to live games, pay-per-view fights, and international tournaments without paying traditional broadcast fees. In this changing environment, crackstreams became one of the most recognized names associated with free sports streaming.
The rise of crackstreams reflects more than simple internet piracy. It reveals how audiences consume entertainment in an era shaped by convenience, instant access, and rising subscription costs. Many viewers became frustrated by fragmented broadcasting rights that forced them to purchase multiple services just to follow their favorite teams or athletes. As a result, platforms like crackstreams attracted enormous attention by offering unofficial live streams for basketball, football, boxing, MMA, and many other sports events.
At the same time, the platform also sparked debates about legality, cybersecurity, copyright enforcement, and the future of sports media. Governments, broadcasters, and league organizations have repeatedly targeted these websites, while users continue searching for replacements whenever domains disappear. The story of crackstreams is therefore not only about free streaming but also about the ongoing conflict between audience demand and media ownership.
What Is crackstreams
crackstreams is a well-known online streaming platform associated with unauthorized live broadcasts of sporting events. The site became widely popular for providing free access to premium sports content that would normally require subscriptions or pay-per-view purchases. Users frequently visited crackstreams to watch NBA games, NFL matchups, UFC fights, boxing events, Formula 1 races, and other major competitions.
READ MORE: zoechip and the Streaming Shift Reshaping Online Viewing
Unlike official streaming platforms, crackstreams did not usually host sports rights directly. Instead, it often acted as an aggregator that connected viewers to third-party streaming sources. This approach allowed the website to rapidly gain popularity among sports fans seeking free alternatives to expensive viewing options.
One reason crackstreams spread so quickly was its simplicity. The website generally offered straightforward navigation, event schedules, and quick-access links before major games or fights. For many viewers, especially younger audiences accustomed to fast online access, the platform felt easier than managing multiple subscriptions across different services.
However, crackstreams has consistently faced legal pressure because it distributes copyrighted sports broadcasts without authorization. Major sports organizations and media companies have targeted such platforms through lawsuits, domain seizures, and takedown requests. As a result, the site has frequently changed domains, disappeared temporarily, or reappeared under new variations.
The Rise of Free Sports Streaming Platforms
The success of crackstreams cannot be understood without examining broader changes in media consumption. Sports broadcasting once relied heavily on cable television networks that controlled exclusive access to live events. Over time, streaming services transformed viewing habits, allowing audiences to watch content on phones, tablets, and laptops from virtually anywhere.
While this shift created convenience, it also introduced financial frustration. A single sports fan might need separate subscriptions for football, basketball, combat sports, and regional matches. Some premium fights also required additional pay-per-view purchases on top of existing monthly fees. For many viewers, especially students and younger audiences, these costs became difficult to justify.
This environment created an opening for platforms like crackstreams. Fans searching online often discovered free streaming communities through social media discussions, forums, or direct recommendations from friends. The appeal was immediate: no contracts, no monthly billing, and instant access to highly anticipated events.
Another factor behind the growth of crackstreams was global accessibility. Official broadcasts are often restricted by country due to licensing agreements. Some viewers could not legally access certain matches in their regions even if they were willing to pay. Unofficial streaming sites removed these geographic barriers, attracting international audiences frustrated by regional limitations.
Why crackstreams Became So Popular
The popularity of crackstreams came from a combination of convenience, timing, and cultural behavior surrounding live sports. Sports fans value immediacy more than almost any other entertainment audience. Missing a championship game or title fight often means losing the excitement of live discussion and social engagement.
crackstreams capitalized on this urgency by making major events available in real time. Users did not need complicated registration systems or lengthy subscription processes. The platform generally focused on speed and accessibility, which aligned perfectly with modern internet habits.
Combat sports contributed significantly to the platform’s visibility. UFC and boxing pay-per-view events can cost substantial amounts for a single night of viewing. crackstreams became widely discussed online because it provided unofficial access to these expensive events. On major fight nights, traffic around the platform often surged dramatically.
Social media also amplified the site’s growth. During large sporting events, users frequently shared streaming links across online communities. Memes, discussion threads, and viral posts turned crackstreams into a recognizable name even among people who had never visited the platform directly.
The platform’s reputation also benefited from changing audience expectations. Modern consumers increasingly expect on-demand accessibility and low-cost entertainment. When official services fail to meet these expectations, many users look elsewhere regardless of legal concerns.
Legal Issues Surrounding crackstreams
Despite its popularity, crackstreams operates in a legally controversial space. Sports broadcasts are protected by copyright laws, and authorized distributors pay enormous amounts for exclusive broadcasting rights. When unofficial platforms redistribute this content without permission, they violate intellectual property protections.
Sports leagues have aggressively fought against unauthorized streaming websites for years. Organizations such as the NFL, NBA, UFC, and major boxing promoters invest heavily in anti-piracy enforcement. Their legal teams regularly issue takedown notices, pursue domain suspensions, and collaborate with internet providers to reduce illegal broadcasts.
One challenge authorities face is the speed at which these sites reappear. Even when a specific crackstreams domain is shut down, mirror sites and alternative versions often emerge quickly. This creates a constant cycle of enforcement and reappearance.
Legal concerns also extend to users in some regions. While enforcement usually targets operators rather than viewers, accessing unauthorized streams can still violate local regulations depending on national laws. Many users underestimate these legal complications because streaming feels less direct than downloading copyrighted files.
The financial impact on sports industries is another major concern. Broadcasters argue that unauthorized streaming reduces subscription revenue and harms the long-term sustainability of sports media rights agreements. Since leagues depend heavily on broadcasting income, piracy remains a serious industry issue.
Cybersecurity Risks and Viewer Concerns
Beyond legality, crackstreams and similar platforms raise important cybersecurity concerns. Unofficial streaming websites frequently rely on aggressive advertising networks, pop-ups, and redirect links to generate revenue. These features can expose users to scams, malware, and deceptive software downloads.
Many viewers are drawn to free streaming without considering potential security consequences. Some mirror sites imitate the appearance of legitimate streaming portals while secretly collecting user information or pushing malicious advertisements. Clicking the wrong link can result in unwanted browser extensions, phishing attempts, or harmful applications.
Cybersecurity researchers have repeatedly warned about fake streaming pages that exploit high-demand sporting events. During championship games or major UFC fights, scammers often create convincing copies of popular streaming platforms to attract desperate viewers searching for live access.
Privacy is another issue surrounding crackstreams. Users may unknowingly expose browsing activity, IP addresses, or personal information when visiting unsecured sites. This has contributed to the growing use of VPN services among online streaming audiences, although VPN usage itself does not legalize unauthorized viewing.
These risks highlight an important reality: free access often comes with hidden costs. While viewers may avoid subscription fees, they can face exposure to security threats that are rarely discussed in casual online conversations.
The Impact on Sports Broadcasting
The existence of crackstreams has influenced the sports broadcasting industry in several indirect ways. Media companies now understand that audiences expect flexibility, affordability, and convenience. Excessively fragmented subscription models can push viewers toward unauthorized alternatives.
In response, some broadcasters have introduced more accessible streaming packages and mobile-friendly viewing options. Sports organizations increasingly invest in direct-to-consumer platforms that allow fans to watch events without traditional cable systems.
The industry has also improved anti-piracy technology. Modern detection systems can identify unauthorized streams faster than in previous years, leading to quicker takedowns during live events. Artificial intelligence tools now help monitor illegal broadcasts across multiple platforms simultaneously.
At the same time, crackstreams demonstrated how passionate sports communities behave online. Fans prioritize accessibility and real-time participation. This lesson has influenced how official platforms design user experiences, especially around live interaction, highlights, and multi-device viewing.
The broader conversation extends beyond piracy alone. Many analysts believe the persistence of sites like crackstreams signals dissatisfaction with current pricing structures in sports entertainment. As long as legal access remains expensive or fragmented, unofficial streaming communities are likely to continue appearing.
The Constant Cycle of Shutdowns and Clones
One of the most unusual aspects of crackstreams is how often the platform disappears and reemerges. Users familiar with the streaming ecosystem understand that domain changes are common. A website may vanish after legal action only to return under a slightly different address days later.
This constant migration has created an entire ecosystem of clone websites, mirror domains, and imitation platforms. Some are connected to original operators, while others are unrelated sites attempting to exploit the popularity of the crackstreams name.
For viewers, this creates confusion and additional risk. It becomes difficult to distinguish authentic versions from malicious copies. Many fake sites use the crackstreams brand simply to attract traffic and advertising revenue.
The repeated shutdown cycle also reveals the limitations of enforcement efforts. Authorities can remove domains, but demand for free sports streaming remains extremely high. As long as audiences continue searching for unauthorized broadcasts, replacement sites are likely to emerge.
This pattern mirrors the broader history of internet piracy. From music sharing services to movie streaming platforms, enforcement has rarely eliminated demand entirely. Instead, platforms evolve, relocate, and adapt to new technological environments.
Why Sports Fans Continue Using crackstreams
Even with legal and security concerns, many viewers continue searching for crackstreams alternatives because of practical frustrations. Sports rights are often divided among numerous broadcasters, making it difficult for fans to follow all events through one affordable service.
International audiences face additional complications. Regional blackouts, exclusive licensing agreements, and delayed broadcasts can prevent viewers from accessing games legally in their locations. Unauthorized streaming sites remove these barriers instantly.
Economic realities also play a role. Subscription fatigue has become increasingly common as entertainment costs continue rising. Some sports fans feel overwhelmed by the number of separate services required to watch different leagues and tournaments.
There is also a cultural aspect tied to internet communities. Many online users grew up during an era when free streaming became normalized across entertainment categories. For some audiences, visiting sites like crackstreams feels less like criminal activity and more like a routine part of online culture.
This does not eliminate ethical or legal concerns, but it helps explain why enforcement efforts alone have not stopped the growth of unofficial streaming communities.
READ MORE: wooflix and the Hidden Reality of Free Streaming
Conclusion
crackstreams became more than a simple streaming website. It evolved into a symbol of changing entertainment habits, rising subscription fatigue, and the growing demand for unrestricted access to live sports. Its popularity revealed major tensions between modern audiences and traditional broadcasting systems.
The platform’s success was driven by convenience, affordability, and global accessibility, particularly during high-profile sporting events. Yet its growth also exposed serious legal, ethical, and cybersecurity concerns. Broadcasters view unauthorized streaming as a direct threat to revenue, while cybersecurity experts warn users about scams and malware risks connected to unofficial sites.
The ongoing cycle of shutdowns and reappearances shows that the issue is far from resolved. As sports broadcasting continues evolving, companies may need to rethink pricing structures and accessibility if they hope to reduce reliance on unauthorized platforms like crackstreams.
Ultimately, the story of crackstreams reflects a larger transformation happening across entertainment media. Technology changed how audiences consume live events, and viewers now expect flexibility, speed, and affordability. Whether official broadcasters fully adapt to those expectations will likely shape the future of sports streaming for years to come.
FAQs
What is crackstreams mainly used for?
crackstreams is mainly known for providing unauthorized live streams of sports events such as NBA games, NFL matches, UFC fights, boxing events, and other major competitions.
Is crackstreams a legal streaming platform?
No, crackstreams operates in a legally controversial space because it distributes copyrighted sports broadcasts without official authorization from rights holders.
Why did crackstreams become so popular?
The platform gained popularity because it offered free and convenient access to premium sports content that would otherwise require expensive subscriptions or pay-per-view purchases.
Are there risks involved in using crackstreams?
Yes, users may face cybersecurity risks such as malware, phishing attempts, fake advertisements, and exposure to unsafe mirror websites when using unofficial streaming platforms.
Why does crackstreams frequently change domains?
crackstreams often changes domains due to legal enforcement actions, copyright complaints, and shutdown attempts by broadcasters and sports organizations.
READ MORE: https://nyweekly.co.uk/
-

 Celebrity1 week ago
Celebrity1 week agoGlynn Daly: The Private Star Behind One of Hollywood’s Most Celebrated Families
-

 Technology6 days ago
Technology6 days agocasîo and the Timeless Reinvention of Everyday Technology
-
 Travel7 days ago
Travel7 days agoNew York and Boroughs: The Real Guide to Understanding NYC Beyond Manhattan
-

 Blogs6 days ago
Blogs6 days agoonnilaina and the Quiet Evolution of Online Expression
-

 Health6 days ago
Health6 days agoObstetrika and the Evolving Science of Safe Childbirth
-
 Travel6 days ago
Travel6 days agolucipara: Hidden Wonders of Indonesia’s Remote Sea Paradise
-
 Blogs6 days ago
Blogs6 days agokääbikud Through Myth, Language, and Modern Imagination
-

 Health3 days ago
Health3 days agoGherkins: The Tiny Pickled Fruit With Global Flavor





