DNSProxy.org DDoS Protection: Safeguarding Your Online Presence
In today’s digital age, where businesses rely heavily on their online presence, the threat of Distributed Denial of Service (DDoS) attacks looms large. These malicious attacks can disrupt services, cause downtime, and tarnish reputations. However, with the right protection in place, such as DNSProxy.org DDoS protection, businesses can safeguard themselves against these threats effectively.
I. Introduction to DNSProxy.org
DNSProxy.org is a leading provider of DDoS protection services, offering comprehensive solutions to mitigate the risks posed by DDoS attacks. With its cutting-edge technology and experienced team, DNSProxy.org helps businesses stay online and operational even in the face of relentless attacks.
DDoS attacks are a prevalent threat in today’s digital landscape, targeting websites, online services, and networks. These attacks aim to overwhelm a target with a flood of traffic, rendering it inaccessible to legitimate users. Without adequate protection, businesses can suffer significant financial losses and damage to their reputation.
II. Understanding DDoS Attacks
What is a DDoS attack?
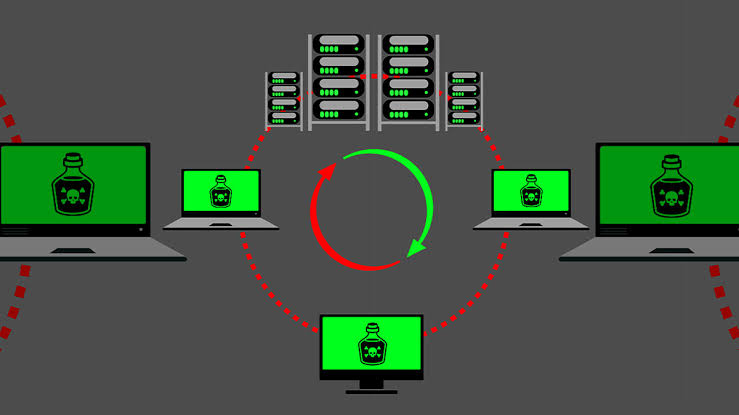
A DDoS (Distributed Denial of Service) attack is a malicious attempt to disrupt the normal traffic of a targeted server, service, or network by overwhelming it with a flood of internet traffic. Unlike traditional DoS attacks, which are carried out using a single source, DDoS attacks leverage multiple compromised systems to launch coordinated attacks.
Different types of DDoS attacks
DDoS attacks come in various forms, including volumetric attacks, which flood the target with a high volume of traffic, protocol attacks, which exploit vulnerabilities in network protocols, and application layer attacks, which target specific applications or services.
How DDoS attacks can disrupt online services
DDoS attacks can have severe consequences for businesses, including downtime, loss of revenue, damage to brand reputation, and potential legal ramifications.These attacks can also be used as a diversionary tactic to mask other cyber threats, such as data breaches or malware infections.
III. The Need for DDoS Protection
In today’s hyper-connected world, where businesses rely heavily on their online presence to reach customers and transact business, the need for robust DDoS protection cannot be overstated. Without adequate protection in place, businesses are vulnerable to DDoS attacks, which can disrupt operations, cause financial losses, and damage brand reputation.
IV. Introducing DNSProxy.org DDoS Protection
DNSProxy.org offers advanced DDoS protection solutions designed to detect and mitigate DDoS attacks in real-time, ensuring uninterrupted access to online services.With its comprehensive suite of features and proactive approach to security, DNSProxy.org helps businesses stay one step ahead of emerging threats.
Features of DNSProxy.org DDoS protection
- Real-time threat detection: DNSProxy.org continuously monitors network traffic for signs of suspicious activity, allowing it to detect and mitigate DDoS attacks as soon as they occur.
- Automatic mitigation: DNSProxy.org automatically reroutes malicious traffic away from the target, ensuring that legitimate users can still access the services.
- Scalability: DNSProxy.org DDoS protection scales dynamically to handle even the largest and most complex DDoS attacks, ensuring uninterrupted service delivery.
- 24/7 support: DNSProxy.org provides round-the-clock support from experienced security professionals, ensuring rapid response to emerging threats.
How DNSProxy.org mitigates DDoS attacks effectively
DNSProxy.org employs a combination of advanced technologies, including traffic filtering, rate limiting, and IP blocking, to mitigate DDoS attacks effectively. By analyzing incoming traffic in real-time and identifying patterns indicative of an attack, DNSProxy.org can take immediate action to block malicious traffic and keep services online.
V. Advantages of Using DNSProxy.org DDoS Protection
Scalability and flexibility
DNSProxy.org DDoS protection is highly scalable, allowing businesses to easily adjust their level of protection to meet changing needs. Whether you’re a small startup or a large enterprise, DNSProxy.org can tailor its services to suit your requirements, ensuring maximum protection without breaking the bank.
Cost-effectiveness
Unlike traditional DDoS protection solutions, which can be expensive to deploy and maintain, DNSProxy.org offers cost-effective protection that doesn’t compromise on security.With flexible pricing plans and transparent billing, DNSProxy.org makes it easy for businesses of all sizes to afford the protection they need.
Easy integration with existing infrastructure
DNSProxy.org DDoS protection is designed to integrate seamlessly with existing network infrastructure, minimizing disruption and simplifying deployment. Whether you’re running on-premises servers cloud-based services or a hybrid environment, DNSProxy.org can protect your assets without requiring major changes to your setup
VI. Case Studies
DNSProxy.org has helped numerous organizations across various industries protect themselves against DDoS attacks and ensure uninterrupted service delivery. From e-commerce websites to financial institutions, DNSProxy.org has proven its effectiveness in mitigating even the most sophisticated attacks.
VII. How to Get Starte with DNSProxy.org DDoS Protection
Getting starte with DNSProxy.org DDoS protection is quick and easy. Simply visit our website, sign up for an account, and choose the level of protection that best suits your needs. Our team of experts will guide you through the setup process and ensure that your services are protected from day one.



